Will Microsoft GCC High Work for CMMC 2.0?
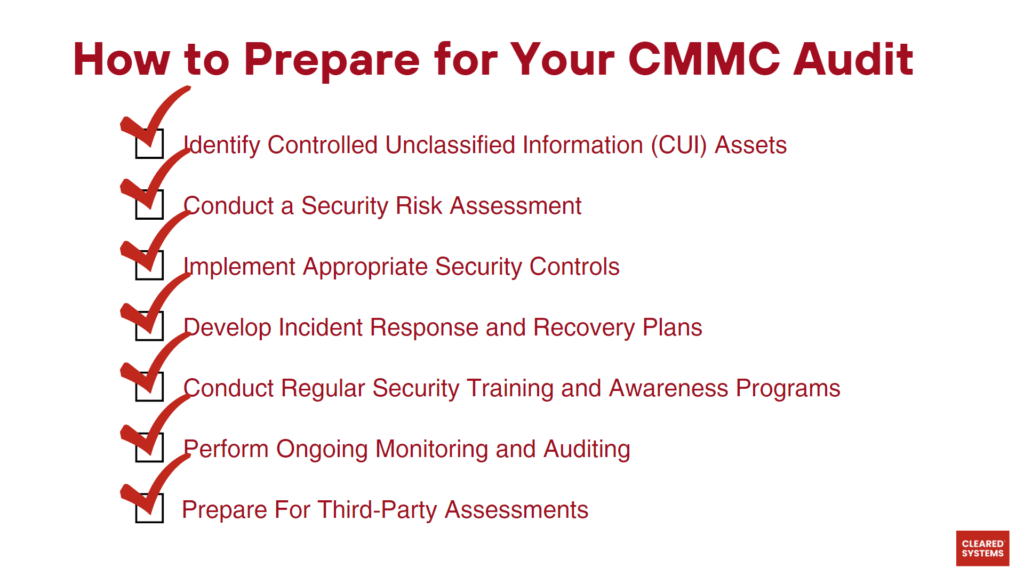
Defense Industrial Base (DIB) has become a target of increasingly complex and frequent cyberattacks. To protect the FCI (Federal Contract Information) and CUI (Controlled Unclassified Information), in November 2021, OUSD A&S announced CMMC 2.0. It aims to dynamically improve the DIB cybersecurity to meet the evolving cyber threats, instill a collaborative culture of cyber resilience and cybersecurity, and ensure accountability while reducing barriers to compliance.